300 companies hired North Korean operatives. What their background checks missed.
In May 2024, the US Department of Justice revealed that more than 300 American companies had unknowingly hired IT workers with direct ties to North Korea. The workers were government operatives, hired under fabricated identities, with a mandate to funnel earnings back to fund state programmes and, in some cases, to access internal systems for intelligence purposes.
The scheme was operationally sophisticated. The operatives deployed VPNs and proxy servers to disguise their location, presented forged identity documents that passed standard verification, and used deepfake technology for video interviews. In some cases, US-based accomplices handled the physical verification steps the remote workers couldn't perform themselves. One security firm tracked over 360 fake personas and more than 1,000 job applications linked to a single operation.
In June 2025, the DOJ announced coordinated nationwide actions: indictments, arrests, and searches of 29 laptop farms across 16 states. Amazon's chief security officer disclosed that the company had blocked over 1,800 suspected North Korean applicants since April 2024, with applications increasing 27% quarter over quarter.
The hiring pipeline, the system every organisation depends on to bring people inside the perimeter, had become an attack vector.

What happened at KnowBe4
The most widely examined case happened in July 2024, and it's worth looking at closely because of what it reveals about the limits of a standard screening process.

KnowBe4 is a cybersecurity company. Its entire business is security awareness training. The company hired a software engineer who completed four video interviews. The candidate's background check cleared. References were verified. The hire was onboarded and given access to company systems.
The candidate was a North Korean operative using stolen US credentials and an AI-enhanced profile photo. After onboarding, the operative installed malware on company systems. KnowBe4's internal security tools detected the activity, and the FBI confirmed the identity fraud.
The company disclosed the incident publicly and offered ten proactive steps for other organisations. The candour was appreciated across the industry. The implication was harder to digest: a cybersecurity firm with dedicated detection tools, above-average awareness of social engineering, and a professional interest in exactly this kind of threat didn't catch it during the hiring process. The fraud was detected after the operative was inside the system, by security software rather than by screening.
Why standard screening didn't catch it
The typical screening process for a technology hire, based on the Veremark Screening Benchmark 2026 data, runs around 3.9 checks per candidate. The check types are balanced across employment verification, academic achievement, references, national ID, and global sanctions.
Database checks (sanctions, criminal record, ID verification) make up a significant proportion. These checks query external registers and confirm whether a document is valid and whether an identity appears on a list. Against a legitimate candidate, this works. Against a well-constructed synthetic identity, built from fragments of real credentials stitched into a fabricated whole, the register returns exactly what the operative intended: no match. The identity is real enough to pass a database check. It's just not the identity of the person using it.
The checks that catch fabrication at higher rates are the verification checks. Employment verification, which contacts previous employers to confirm dates, title, and role, breaks down when the listed employer has no record of the person. Education verification breaks down when the institution can't confirm the claimed qualification. CV gap analysis, which maps the full career timeline against verified dates, surfaces the inconsistencies that appear when a career history has been assembled from fragments rather than lived.
Across the Veremark dataset, employment checks flag discrepancies in roughly 1 in 7 candidates. Education checks flag in 1 in 5. CV gap checks flag in more than 1 in 2. Database checks flag in fewer than 1 in 100. The checks designed to confirm register entries work against legitimate identities. The checks designed to verify career claims are where fabrication becomes visible.
The threat is scaling
The DOJ findings describe an operation that was already running at significant scale in 2024, and the indicators suggest it's growing.
Amazon blocked over 1,800 suspected applicants in roughly 18 months, with the rate of applications increasing 27% quarter over quarter. Gartner projects that by 2028, 1 in 4 candidate profiles worldwide could be fake. Resume Genius found that 17% of hiring managers had encountered suspected deepfake interviews by end of 2024, up from 3% the year before. The Citi Institute projects 8 million deepfakes online by end of 2025, up from roughly 500,000 in 2023. The Federal Trade Commission reported that losses from job-related fraud rose from $90 million in 2020 to $501 million in 2024.
The North Korean operation is the most documented example, but the infrastructure it relies on (synthetic identities, deepfake video, fabricated career histories, US-based proxies for physical verification) is increasingly available to a wider range of actors. The tools are cheaper and more accessible with each passing year. The hiring pipeline is an attractive target because it's designed around trust by default: a candidate applies, presents credentials, passes checks, and is given access to systems. The verification process is the only barrier, and when that process is built primarily around database checks, the barrier has a known weakness.
The legal exposure is shifting
Negligent hiring liability holds employers responsible when they knew, or should have known, of an employee's unsuitability at the time of hire.
Two years ago, hiring a state-sponsored operative through a faked remote application might have been treated as an unforeseeable event. After FBI advisories, DOJ enforcement across 16 states, the KnowBe4 disclosure, and extensive media coverage, the "should have known" threshold has moved. Employers are now on notice that this threat exists, that it targets remote technology roles specifically, and that standard database screening is insufficient to detect it.
For an employer that relies on a default screening package for remote technical hires with access to production systems, customer data, or source code, the argument that the risk was unforeseeable is becoming increasingly difficult to sustain. The question a court or regulator would ask is straightforward: given the public warnings, what additional verification steps did the organisation take for roles with elevated access?
What the screening response looks like
The threat doesn't require an overhaul of the entire hiring process. It requires specific, targeted strengthening for the roles where the exposure is highest.
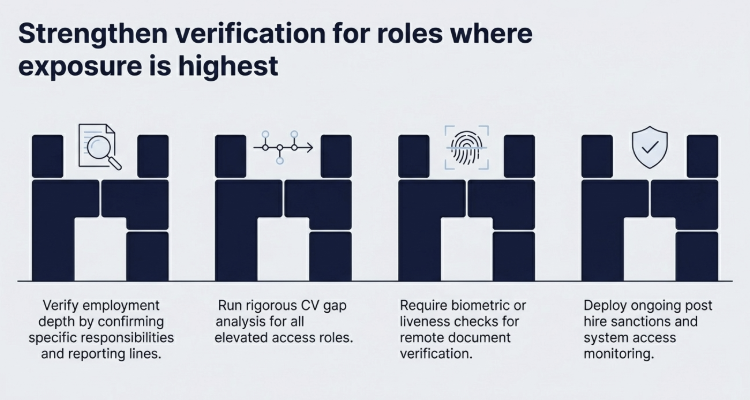
Employment verification depth matters more than breadth.
For roles where the claimed career history is the primary basis for the hire, confirming dates and title is a starting point. Going further, confirming responsibilities, reporting lines, and the reason for leaving, reduces the surface area for fabricated histories. The Veremark data shows employment verification flagging discrepancies in 1 in 7 candidates. A fabricated employment history, constructed from scratch rather than embellished from real experience, is more likely to fail deeper verification because there's no legitimate employer at the other end to confirm any of it.
CV gap checks for roles with elevated access.
At more than 1 in 2, CV gap analysis flags issues more often than any other check type. A fabricated career timeline often produces gaps that don't hold together when the full history is mapped against verified dates. For roles with access to production systems, customer data, or intellectual property, this check addresses the narrative layer where synthetic identities are most likely to show inconsistencies.
Identity verification beyond documents.
Standard ID checks confirm whether a document is valid. They don't confirm whether the person presenting it is the person it belongs to. For remote hires who will never be physically present, biometric or liveness-based verification addresses the gap that document checks cannot. The KnowBe4 operative passed standard ID verification using stolen credentials. The fraud was in the person, not the document.
Post-hire monitoring for system-access roles.
The DOJ findings showed operatives maintaining positions for months before detection. Ongoing sanctions monitoring, adverse media checks, and system access reviews can surface issues that the onboarding check missed or that develop after hire. The KnowBe4 case was ultimately caught by internal security tooling, not by screening. For organisations without that level of internal detection capability, ongoing screening provides a different layer of monitoring.
The hiring pipeline was designed for a world where candidates were who they said they were. That assumption no longer holds at the scale and sophistication the DOJ findings describe. The screening process doesn't need to be rebuilt from scratch. It needs to be adapted for the roles where the threat is real and documented, with verification methods that test the things synthetic identities are designed to survive.
The data behind this article comes from the Veremark Screening Benchmark 2026. The full report covers discrepancy rates across check types, industry screening profiles, and a framework for assessing programme effectiveness.
{{the-2026-veremark-screening-benchmark="/components"}}
FAQs
This depends on the industry and type of role you are recruiting for. To determine whether you need reference checks, identity checks, bankruptcy checks, civil background checks, credit checks for employment or any of the other background checks we offer, chat to our team of dedicated account managers.
Many industries have compliance-related employment check requirements. And even if your industry doesn’t, remember that your staff have access to assets and data that must be protected. When you employ a new staff member you need to be certain that they have the best interests of your business at heart. Carrying out comprehensive background checking helps mitigate risk and ensures a safer hiring decision.
Again, this depends on the type of checks you need. Simple identity checks can be carried out in as little as a few hours but a worldwide criminal background check for instance might take several weeks. A simple pre-employment check package takes around a week. Our account managers are specialists and can provide detailed information into which checks you need and how long they will take.
All Veremark checks are carried out online and digitally. This eliminates the need to collect, store and manage paper documents and information making the process faster, more efficient and ensures complete safety of candidate data and documents.
In a competitive marketplace, making the right hiring decisions is key to the success of your company. Employment background checks enables you to understand more about your candidates before making crucial decisions which can have either beneficial or catastrophic effects on your business.
Background checks not only provide useful insights into a candidate’s work history, skills and education, but they can also offer richer detail into someone’s personality and character traits. This gives you a huge advantage when considering who to hire. Background checking also ensures that candidates are legally allowed to carry out certain roles, failed criminal and credit checks could prevent them from working with vulnerable people or in a financial function.
Trusted by the world's best workplaces






APPROVED BY INDUSTRY EXPERTS
.png)
.png)




and Loved by reviewers
Transform your hiring process
Request a discovery session with one of our background screening experts today.







